Stone
10k Member
I have UAC disabled! 
| VCF West | Aug 01 - 02 2025, | CHM, Mountain View, CA |
| VCF Midwest | Sep 13 - 14 2025, | Schaumburg, IL |
| VCF Montreal | Jan 24 - 25, 2026, | RMC Saint Jean, Montreal, Canada |
| VCF SoCal | Feb 14 - 15, 2026, | Hotel Fera, Orange CA |
| VCF Southwest | May 29 - 31, 2026, | Westin Dallas Fort Worth Airport |
| VCF Southeast | June, 2026 | Atlanta, GA |
Which is because, unfortunately, it's basically impossible to get anything done on Windows if you aren't running with administrative privileges. Moreso on Vista and up, where UAC locks things down tighter than a dirty simile if you're not running as admin, but even on XP it's more trouble than it's worth.
It doesn't matter if the malware makes it into an AV database. The antivirus program won't be able to recognize it anymore if you modify it even the slightest. Now, consider how many iterations of the same code you can create just by doing simple things like changing the order of instructions or changing the encoding of instructions. Each little change is a new variation that has to go in the AV database. Now slap on some compression and/or encryption and we are up to how many combinations of that single virus?
Yeah, I get that. On the other hand, the key reason I'm using open-source antivirus software is because I can be reasonably sure it's never going to turn into nagware and/or dominatrixware like so many commercial antivirus programs have, because it would get forked if it did.One thing I don't understand, though, is open-source antivirus software. That's like installing an alarm system in your house, and posting the wiring diagram on the door...
MSE is still very much current--I routinely get updates on my system (POSReady 2009 Registry key). It's probably the same signature data distributed for Win7 and Vista users. The July 2015 "update" (4.5) essentially disables MSE for XP, so just re-install using a 4.4x or 4.3x version.
One thing I don't understand, though, is open-source antivirus software. That's like installing an alarm system in your house, and posting the wiring diagram on the door...
As to Windows - I turned off XP updates after SP3 and have never had, or seen, a single problem that wasn't picked up by AV software and easily cured. Decent firewall and AV protection is far more effective than the endless grind of dubious automatic updates. But I'll let Win10 do its update thing on a pilot machine to see how that shapes up in bandwidth v. risk management.
I found that it's generally useful to use the "unofficial SP4" ISO on a new XP installation after installing SP2. Covers a lot of nits.
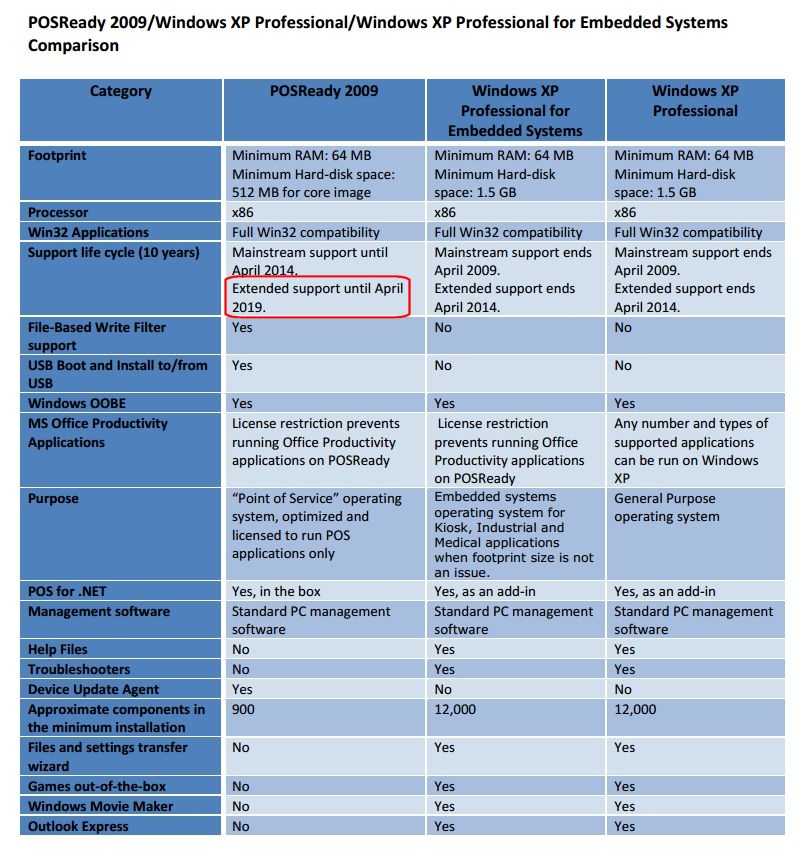
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\WPA\PosReady]
"Installed"=dword:00000001I've thought about maybe building a machine with XP on for running (heavily?) modded Fallout 3 and Fallout NV games, but I don't have any money to do it and I'd rather save my money for getting into vintage hardware..
Usually there's absolutely nothing wrong with them, except maybe some malware and junk apps clogging up the hard drive.
Discarded Windows XP machines are plentiful these days. Snoop around your local e-waste dropoff point or recycling center on weekends and you're almost always guaranteed to find a few old Pentium 4 machines that people drop off for recycling. Usually there's absolutely nothing wrong with them, except maybe some malware and junk apps clogging up the hard drive.